How eComplete drives measurable impact with a lean, Weld-powered data stack
“Weld gives us the ability to see a huge array of KPIs and data points that we can then feed back to clients in an insightful and actionable way.”

Chat, docs, email, and system updates — all in one place.
SUPPORT
Reach us by email — we usually respond same business day.
Explore setup guides, tutorials, and best practices.
Find answers to frequently asked questions.
Step-by-step to your first pipeline.
Sign up to start a guided product tour.
Plans, row allowances, and add-ons.
Read our terms for using Weld.
Review our DPA for data protection.
Learn about Weld’s security practices.
Understand how we handle and protect your data.
Review our SLA commitments.
FAQ
Can’t find what you’re looking for? Reach out via the website chat.
CUSTOMER STORIES
“Weld gives us the ability to see a huge array of KPIs and data points that we can then feed back to clients in an insightful and actionable way.”

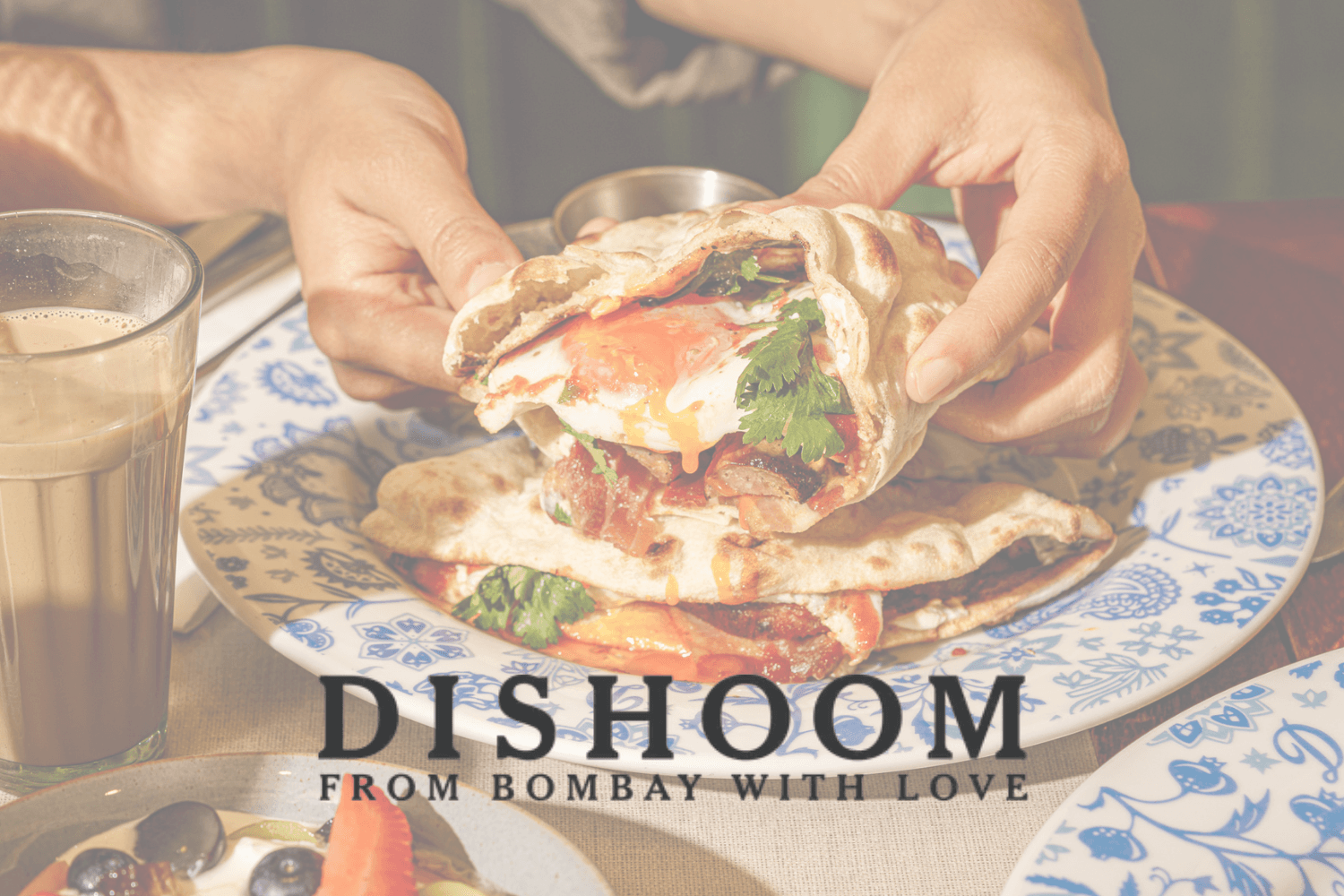
“One of the biggest impacts has been unlocking new ways to buy media. Before, we didn’t have the data to back up strategic decisions – now we do.”

“Before Weld, we had to rely on custom Python scripts and manual processes that were time-consuming and error-prone.”

“We’re still a team of three, but we’re often doing far more than the equivalent of three full-time employees. That’s down to how we're able to leverage systems, data, and processes.”
“We’ve always been a KPI-driven company. But we wanted to scale that mindset across every team member, every team, every decision.”

“Before Weld, our data infrastructure was limited and we relied heavily on Excel files and custom Python scripts.”

“Weld has saved us a ton of time, from not having data ready to having a fully functional data warehouse and connectors.”
SECURITY
WHITE PAPER
Our approach to security, compliance, and privacy — covering SOC 2, SOC 3, ISO 27001, HIPAA readiness, encryption practices, and governance.

Independent audit of security controls over time. Report available under NDA.

ISO 27001-certified infrastructure and ISMS practices.

HIPAA-ready processes and controls for PHI where applicable.

TLS 1.2+ in transit and strong encryption at rest.

SSO/MFA and role-based permissions with least privilege.

Privacy-first by design with EU data residency options.
Spend less time managing data and more time getting real insights.